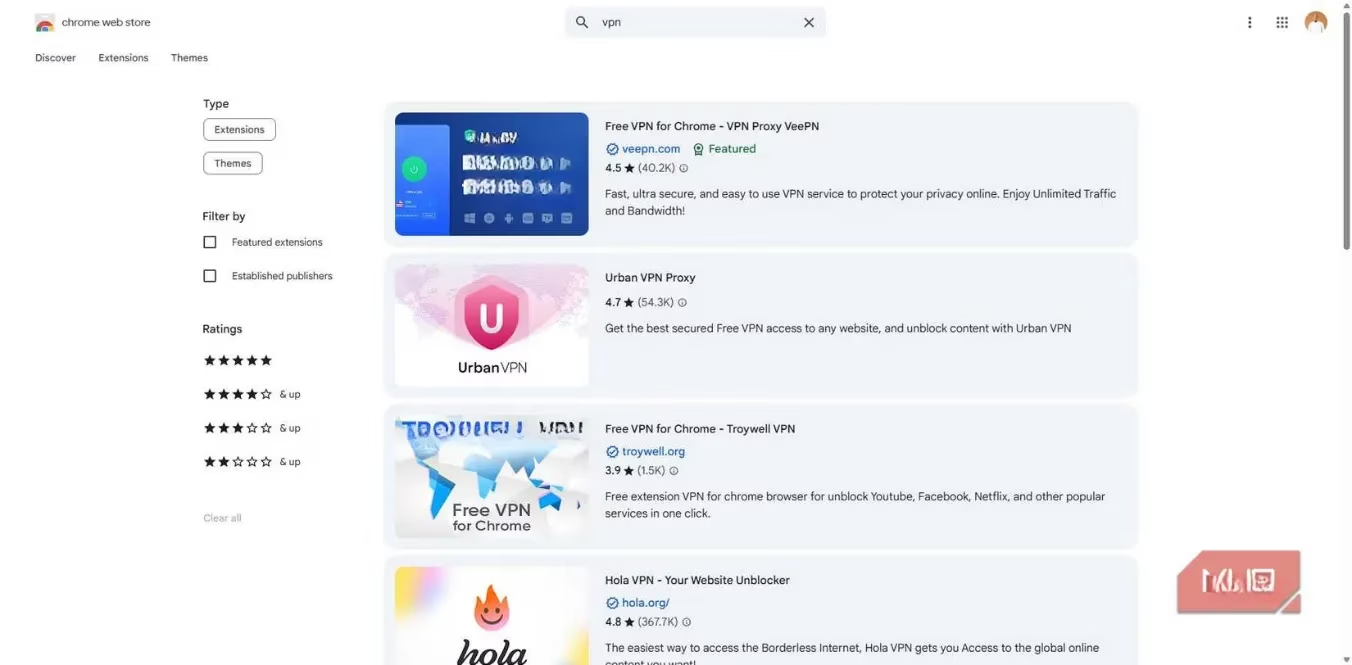
In the ever-evolving digital landscape of 2026, the promise of privacy and security remains paramount for users worldwide. Having evaluated countless virtual private networks over the years, one truth stands clear: a VPN that fails to encrypt data, mask IP addresses, and conceal location is fundamentally failing its core mission. While the Chrome Web Store and Firefox Add-ons marketplace are flooded with VPN browser extensions, a critical examination reveals these tools often offer little more than a facade of protection. Many are merely proxies with sophisticated branding, incapable of safeguarding your privacy. Similarly, VPNs built directly into browsers present their own set of risks. For individuals who genuinely value their data security, relying on these browser-based solutions is a perilous compromise.
The Fundamental Flaws of Browser VPNs
A robust VPN must fulfill four essential functions: 1) encrypt all internet traffic, 2) hide your location by masking your IP address, 3) prevent DNS leaks to keep browsing private, and 4) include a kill switch to halt traffic if the VPN connection drops. Browser VPNs, however, consistently fall short of this standard. Their most significant limitation is that they typically encrypt traffic only within the browser itself. This creates a dangerous false sense of security, as every other application on your device—from email clients and messaging apps to system updates—continues to transmit data in an unencrypted, vulnerable state. Your Internet Service Provider (ISP) and potential eavesdroppers can still see a substantial portion of your digital footprint.
-
Limited Scope: Desktop applications like Spotify, Zoom, or project management tools operate outside the browser's tunnel. Their connections bypass the VPN entirely, exposing your activity and the domains you connect to.
-
Technical Misnomer: What is commonly marketed as a "browser VPN" is, in technical terms, often an HTTPS proxy. These proxies only reroute browser traffic, leaving all other system applications fully exposed. Legacy or specialized clients (e.g., FTP, IRC) are not designed to use such proxies and will never be protected.
The Hidden Cost of "Free" Protection
If the incomplete protection were the only issue, it might be a calculated risk. However, a more alarming problem lies in what these services actively collect. 🚨 Numerous browser VPNs advertise "no-logs" policies, free access, and military-grade encryption, yet their privacy policies frequently tell a contradictory story. As the adage goes, when a product is free, you are often the product.
Independent audits, such as the report from The Best VPN, have highlighted that many popular browser extensions—including Hola VPN, Hotspot Shield, and Betternet—log sensitive data like browsing history, original IP addresses, connection timestamps, and bandwidth usage. Even in cases where the VPN component itself is audited and trustworthy, like Opera's built-in VPN, the overarching browser privacy policy can undermine user privacy. Opera's policy, for instance, states it collects IP addresses, browser details, general location, and pages visited for advertising, analytics, and cross-device tracking. This practice is far from unique; it underscores a systemic issue where the vessel (the browser) can negate the privacy benefits of its tool (the VPN).
Furthermore, the browser extension ecosystem is rife with VPNs listed under shell companies without verifiable corporate addresses. In an industry where trust is the cornerstone, these opaque operations raise immediate red flags regarding data handling and ultimate accountability.
Performance Pitfalls and Functional Limitations
Beyond privacy concerns, browser VPNs often deliver a subpar user experience. Performance typically takes a significant hit due to overcrowded, limited server infrastructure. Simple tasks like loading webmail or streaming video can become frustratingly slow as thousands of users compete for bandwidth on shared servers.
| Feature | Premium Full-Device VPN | Typical Browser VPN |
|---|---|---|
| Encryption Scope | System-wide (all apps) | Browser-only |
| Server Selection | Optimized for streaming, gaming, torrenting | Limited, generic servers |
| Performance Impact | Minimal with premium providers | Often significant slowdowns |
| Geo-restriction Bypass | Highly effective | Unreliable, frequent disconnects |
Most browser VPNs lack the ability to select servers optimized for specific tasks—such as reducing latency for gaming or accessing region-locked streaming content. This results in an instantly limited and often frustrating online experience, making them ineffective tools for anything beyond the most basic web browsing.
Superior Alternatives for Real Security in 2026
Given the shortcomings of browser VPNs, what are the effective alternatives for users seeking genuine privacy? Several robust solutions have solidified their reputations.
-
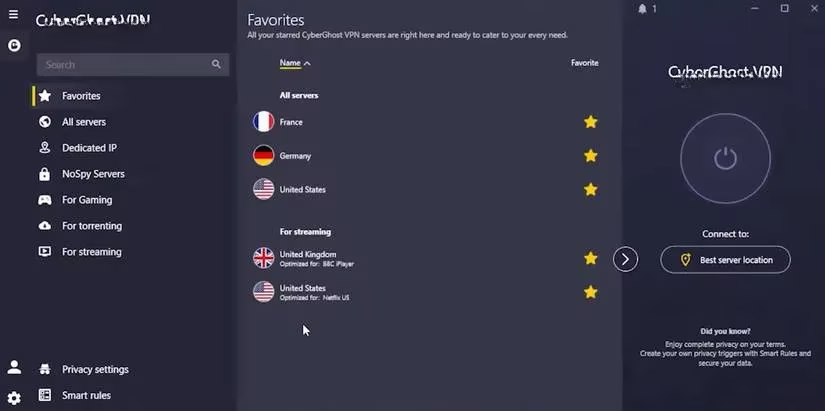
Full-Device VPNs: 👑 This is the gold standard. Services like Mullvad and IVPN are highly recommended for their transparent, audited no-logs policies and commitment to privacy—they do not require personal information to create an account. These VPNs encrypt traffic from your entire device, ensuring every application is protected.
-
DNS-Level Protection: Tools such as NextDNS or AdGuard provide a critical layer of defense that operates at the system level, beneath the browser. They filter DNS queries to block trackers, malicious domains, and ads before a connection is even fully established on your device.
-
Self-Hosted VPN Server: For maximum control and transparency, setting up your own WireGuard or OpenVPN server on a virtual private server (VPS) or home network is the ultimate solution. While it requires technical knowledge, it guarantees you have complete authority over your data path.
The Final Verdict
So, would a privacy-conscious expert ever recommend a standalone browser VPN in 2026? The answer is a resounding no—with one specific exception. A browser extension is acceptable only if it is a complementary component of a trusted, full-device VPN subscription, such as those offered by NordVPN or similar reputable providers. In this configuration, the extension merely provides convenient browser control for a service that is already protecting your entire system.
Anything less than a full-device solution is a half-measure. In the critical realms of digital privacy and security, half-measures are tantamount to no measures at all. It is also crucial to remember that VPN protection should extend beyond your computer. In 2026, smartphones, tablets, and smart home devices all transmit data and possess unique IP addresses, making them equally vulnerable. A comprehensive security strategy employs robust, system-wide VPN protection across all internet-connected devices to ensure a truly private and secure digital life.
