In 2026, if you ask the average person how they maintain privacy online, you'll likely hear a familiar chorus: "I use incognito mode," "I always reject cookies," or "I switched to a privacy browser." These actions feel responsible, creating a comforting illusion of control in a digital world that feels increasingly invasive. Yet, the harsh reality is that most of these common practices offer little to no meaningful protection against modern tracking techniques. The myths persist because they require minimal effort or understanding, but they leave users far more exposed than they realize, clinging to outdated ideas while sophisticated data collection operates in the background.
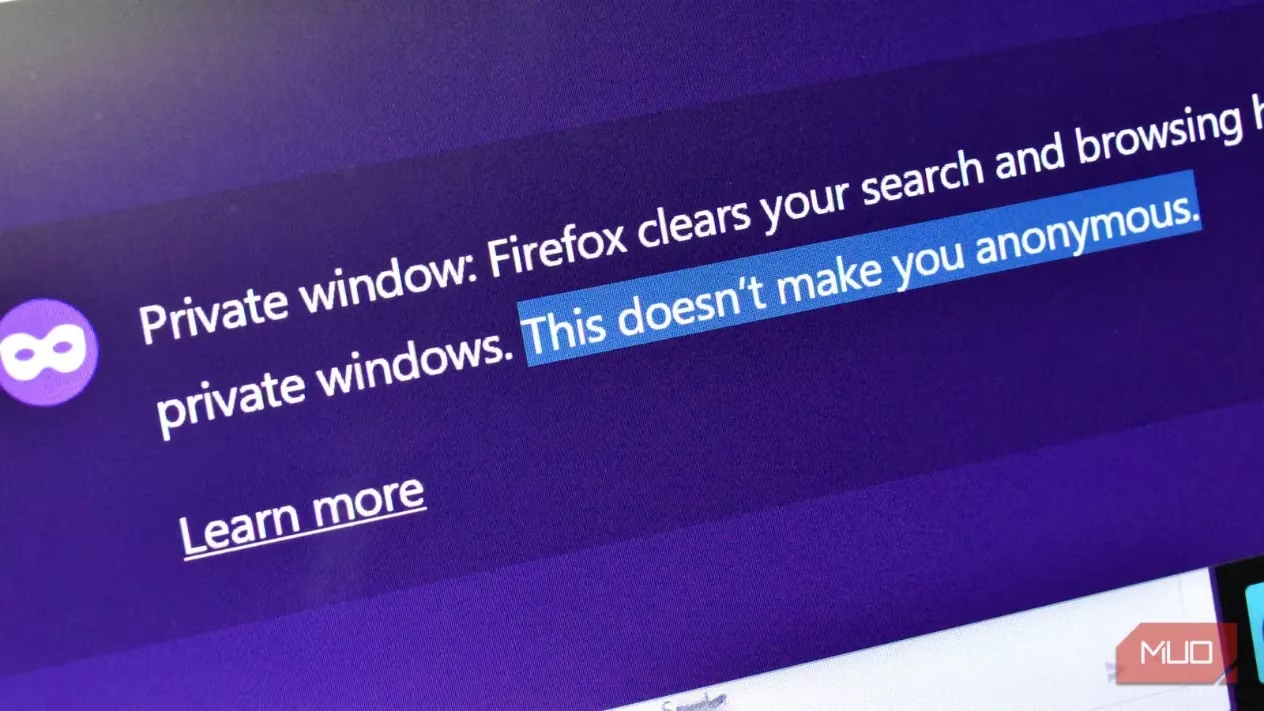
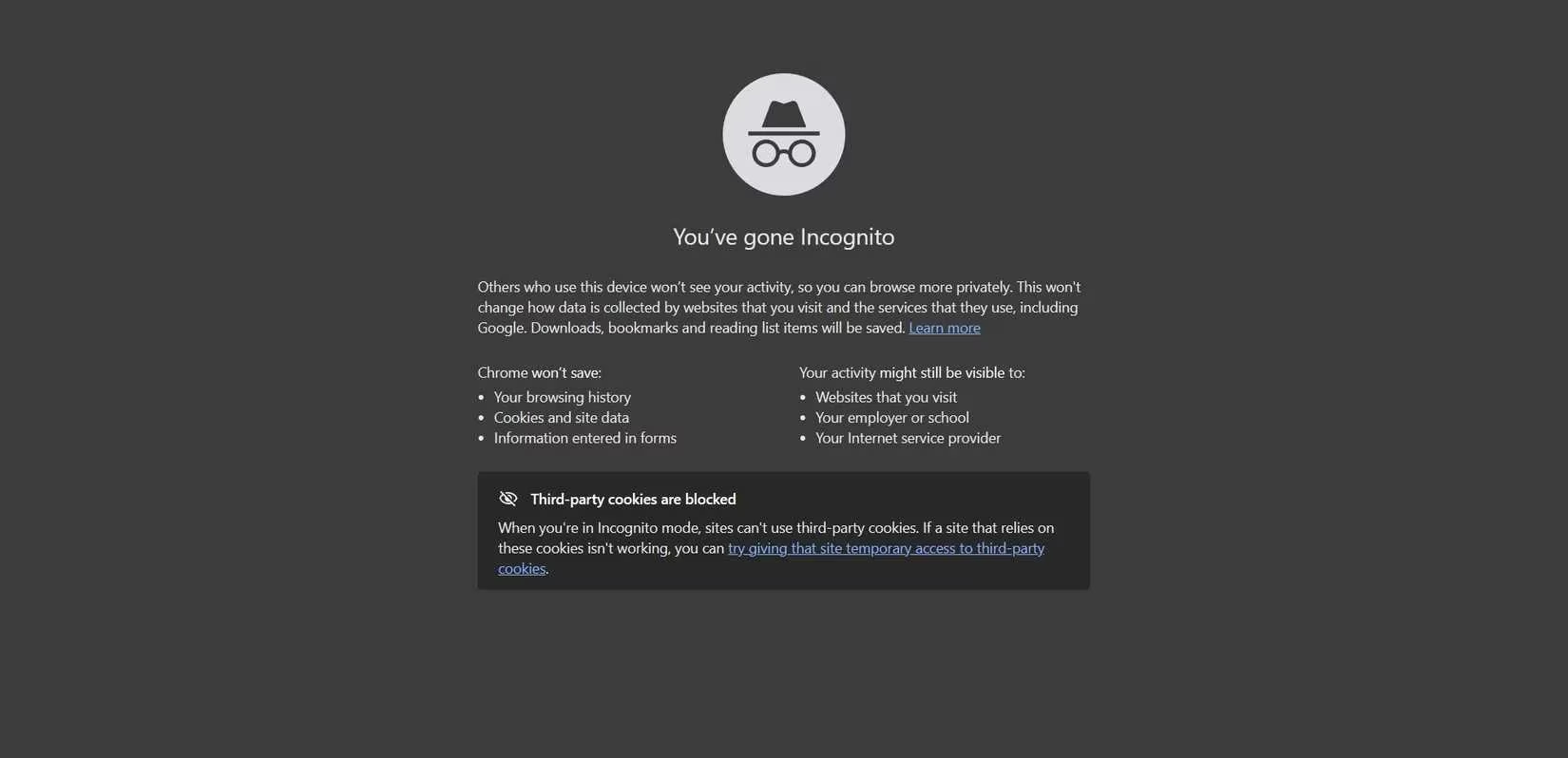
Let's start with the most pervasive myth: the magical privacy of incognito or private browsing. This feature does precisely three things: it doesn't save your browsing history locally on your device, it isolates cookies for that specific session, and it deletes them when you close the window. That's the full extent of its power. 😮 It does not hide your activity from:
-
The websites you visit
-
Advertisers and data brokers
-
Your internet service provider (ISP)
-
Your employer or school network administrator
-
The browser vendor itself (like Google or Microsoft)
When you open an incognito tab, the website you visit still receives a wealth of information: your IP address (which can reveal your approximate location), detailed device specifications, your screen resolution, a list of installed fonts, your timezone, and intricate behavioral patterns. Tracking scripts execute normally. Browser fingerprinting—a technique that creates a unique identifier based on your device's configuration—works perfectly. If you make the critical mistake of logging into any account, like Google or Facebook, your entire session becomes fully attributable to you, completely negating the incognito facade. Part of the confusion stems from the naming itself; terms like "incognito" and "private" suggest invisibility, while the small-print warnings about limited protection are easily overlooked.
Another ritual born from regulatory compliance, not user empowerment, is the constant clicking of "Reject All" on cookie consent banners. These ubiquitous pop-ups have trained us to believe that rejection is a powerful privacy gesture. In reality, it's a minor speed bump for trackers. While rejecting third-party cookies can help a little, modern surveillance has evolved far beyond them. Websites now heavily rely on a suite of alternative methods:
-
Browser Fingerprinting: Creating a unique profile from your device's characteristics.
-
Server-Side Tracking: Logging your activity directly on the website's own servers.
-
Session Correlation: Linking your actions across different pages and visits.
-
Account-Based Analytics: Tying everything you do to your logged-in identity.
Crucially, none of these advanced techniques require traditional third-party cookies. By simply using a website or service, you often give implicit approval for these other forms of data collection, regardless of your cookie preferences. The banners exist primarily to satisfy laws like the GDPR, not to serve as a robust privacy shield.
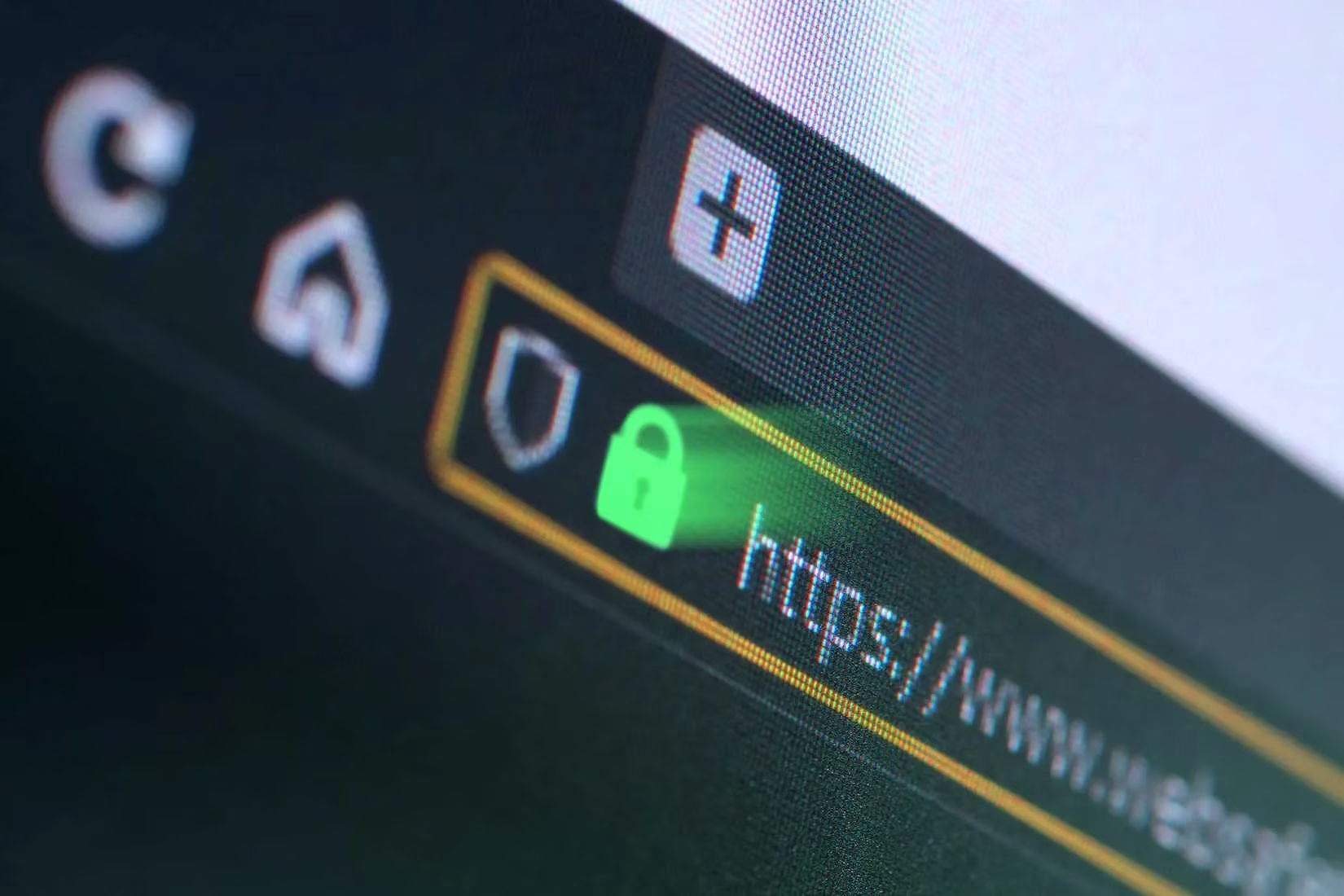
Then there's the symbol many still trust: the HTTPS padlock in the address bar. Its prominence has even been reduced in browsers like Chrome, as companies recognized it was fostering a false sense of security. ✅ It is true that HTTPS (the 'S' stands for Secure) encrypts the data between your browser and the website, preventing thieves from stealing your information in transit. This is vital for protecting passwords and credit card details. However, HTTPS does nothing to prevent:
-
Cookies from being placed on your device
-
Fingerprinting scripts from running
-
The website itself from collecting and selling your behavioral data
The connection is secure, but the tracking on the other end is fully operational.
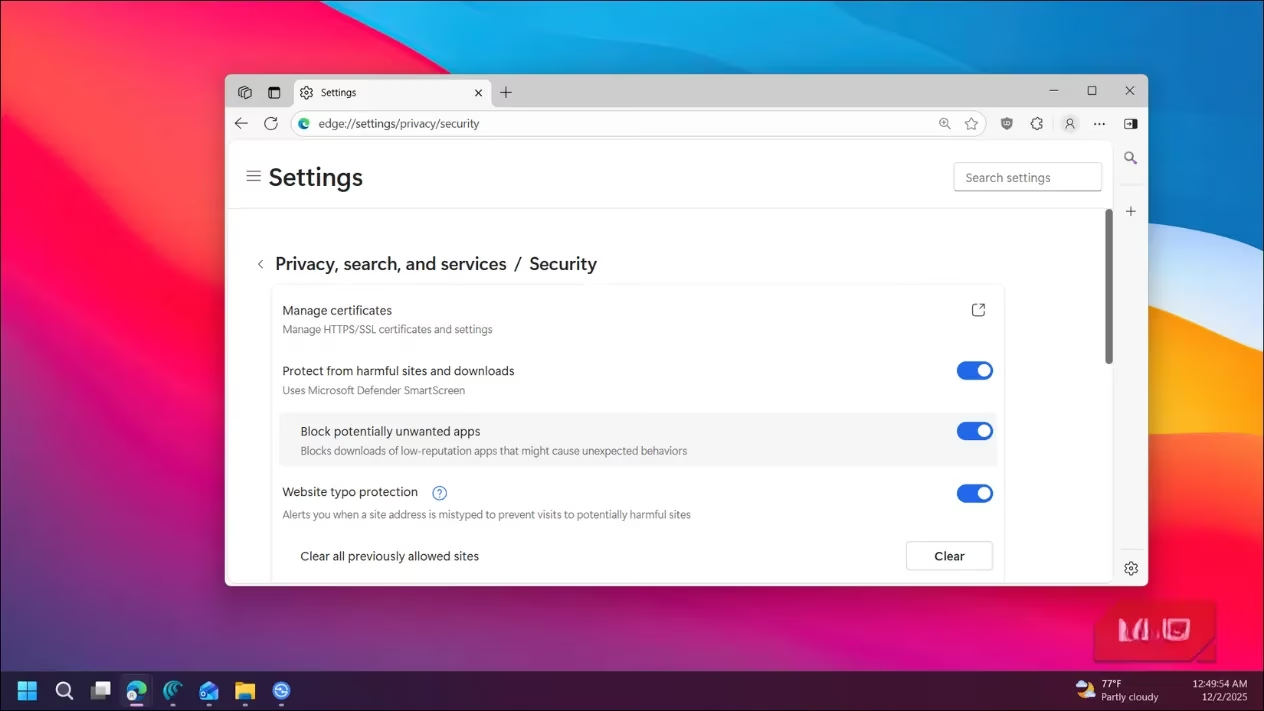
Modern browsers have undoubtedly improved. Features like tracking protection, cookie partitioning, and enhanced permission prompts are steps in the right direction. However, their default settings represent a compromise between privacy, website compatibility, performance, and the economic reality of the online advertising ecosystem. Built-in protections typically rely on blocklists to stop known trackers, but they are often ineffective against:
-
Novel or first-party tracking scripts
-
Obfuscated code designed to evade detection
-
Correlation techniques that use non-blocked data points
These defaults reduce the background noise but fail to prevent a determined tracker from stitching together your digital identity across multiple sites using the stable signals your browser inevitably leaks.
This isn't to say privacy-focused browsers like Brave or Firefox with hardened settings are pointless. They are significantly better than using a data-hungry default Chrome setup or the new wave of "AI-browsers" like ChatGPT Atlas and Perplexity Comet, which often prioritize data collection for model training under the guise of assistance. 🛡️ The core issue arises when behavioral patterns undermine the technology. If you use a privacy browser but then log into centralized services like Amazon, Meta, or Microsoft, you are voluntarily re-attaching your identity to your browsing activity. It's analogous to using the ultra-private Tor Browser to check your Facebook account—Facebook still knows exactly who you are and what you're doing.
So, what actually works? The most effective strategy shifts focus from rituals to source-level prevention. Since a browser is necessary for navigating the web, the goal is to minimize the data it can collect in the first place. A powerful and highly recommended approach is using a dedicated script-blocking tool. These tools don't just hide ads; they prevent the tracking scripts from ever loading and executing on your device.
For most users, browser extensions offer a great balance of ease and effectiveness:
| Extension | Best For | Key Benefit |
|---|---|---|
| uBlock Origin Lite | Everyday users seeking strong protection with low resource use. | Efficiently blocks ads, trackers, and malware domains. |
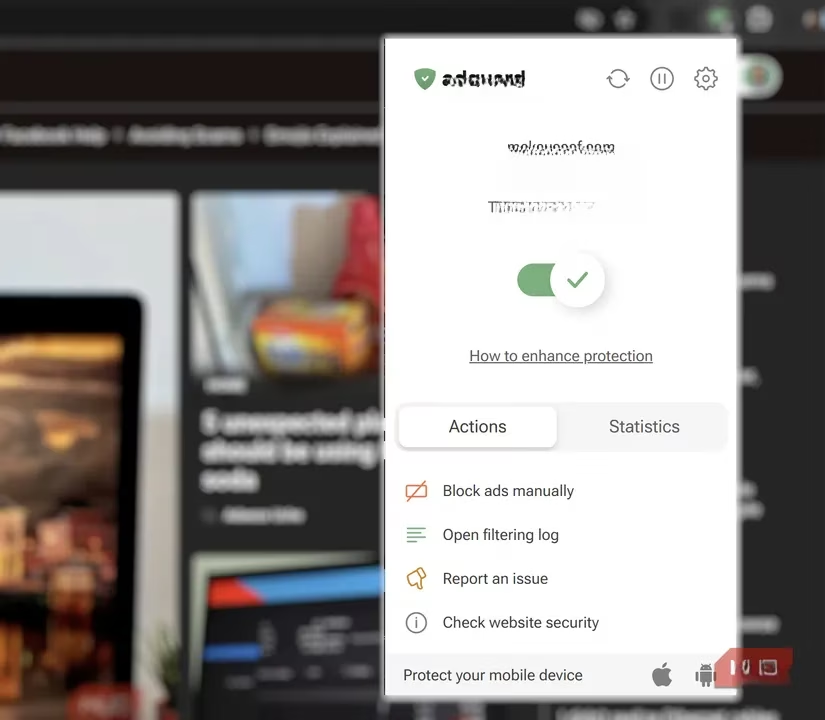
| AdGuard AdBlocker | Those wanting a user-friendly interface with customizable filters. | Blocks ads, tracking, and phishing sites across all tabs. |
For users seeking maximum control and power, NoScript is the open-source gold standard. It takes a "block all scripts by default" approach, allowing you to permit them on a trusted site-by-site basis. This method blocks a vast array of tracking, fingerprinting, and malicious scripts. It's so effective that it's a core component of the privacy-centric Tor Browser.
The landscape of online privacy in 2026 is defined by a gap between perception and reality. Comforting myths about incognito mode, cookie rejections, and HTTPS padlocks persist because they are simple. True privacy, however, requires moving beyond these illusions. It demands an understanding that tracking is a systemic feature of the modern web, not just a few cookies. Effective protection comes from a combination of better tools—like script blockers and privacy-conscious browsers—and smarter behavior, such as minimizing logins to major tracking corporations and being selective about what services you use. You don't need to disappear from the internet, but you do need to stop believing in digital fairy tales and start implementing strategies that address how tracking actually works.
Recent industry context is highlighted by Forbes - Games, and it’s a useful reminder that “privacy” features in mainstream platforms often double as marketing while still fitting neatly into ad-funded business models—mirroring how browser myths like incognito mode or cookie rejections can feel protective but fail against modern tracking and identity-based analytics that operate behind the scenes.
